Anti-Counterfeit Labels
At Whitlam Label, we understand that protecting your brand is an important asset that can require a custom-built solution that meets your product’s needs. Security labels incorporate a combination of properties to address multiple threats. A layered security is the only proven approach that can provide a means for protecting your brand image.
Did you know…?
- Counterfeit and pirated goods is a half-trillion-dollar industry and increasing.
- Every year counterfeit goods, private goods, and theft cost the American economy as much as $700 billion a year
- The counterfeit and pirated goods market has risen steadily in the past few years and as of 2021 it was 2.5% of the world trade

WHITLAM HAS THE SECURITY MEASURES TO SAFEGUARD YOUR PRODUCTS

Tamper Evident
Tamper Evident labels are destructible papers and films which can change appearances or are destroyed when an attempt is made to remove them or to transfer them onto other products.
The primary function of tamper evident or tamper resistant labels is to indicate or prevent alterations by tampering and/or indicate that an article is genuine and fit for use.
Solutions include:
- Tamper Indicating Solutions
- Tamper Evident Solutions
- Destructible Solutions
- Temperature Indicating Solutions
What is the Effectiveness Of Our Tamper-Evident Labels.
The effectiveness of our tamper-evident labels is significant in preventing unauthorized access and ensuring product integrity. Whitlam anti-counterfeit labels are designed to disintegrate or leave visible markings when tampered with, making it easy to identify any unauthorized attempts to open or alter the product. They serve as a reliable security measure for various industries, including pharmaceuticals, food, and consumer goods, by deterring tampering and providing peace of mind to both businesses and consumers.

Authentication
Anti-counterfeit labels incorporate specific properties or combinations of security features (such as overt & covert) into the face material as a mean of authentication. These labels are difficult to reproduce, and depending on the level of security used, their authenticity can be checked by brand-owners, the government, and the public at any point within the supply chain. Whitlam offers an assortment of technologies available to combat counterfeiting.
- We aim to develop the highest possible level of security with optimum cost.
- We look at combining low and high security elements together to enhance protection. Ex. Security inks + security paper + hologram
- We use different types of security technologies to maximize counterfeit protection.
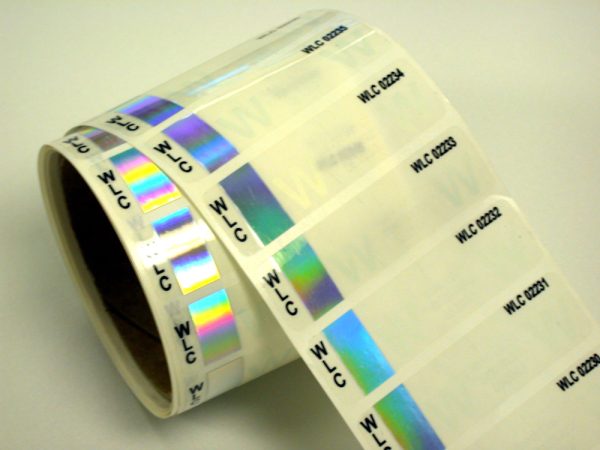
Overt Technologies
Overt technology features are authentication devices built into labels and/or packages which are visible and show dynamic visual effects. Overt technologies include barcodes, specialty inks and labels, holograms, watermarks, embossing, tamper-evident film, and more.
Overt security technologies can be combined with other technologies for multi-layered anti-counterfeiting solutions. Whether it’s a singular overt solution, or a combination of overt, covert, and other solutions, Whitlam can help.
Covert Technologies
Covert technology is not visible to the human eye. Covert features do not enable instant authentication of products or identification through visual inspection by the user. Covert devices can be made more secure by combining them with overt features to deliver the benefit of both systems. This can include multiple covert technologies, such as invisible inks and/or taggants that are in the packaging or product, which can only be read with proprietary readers or detectors.
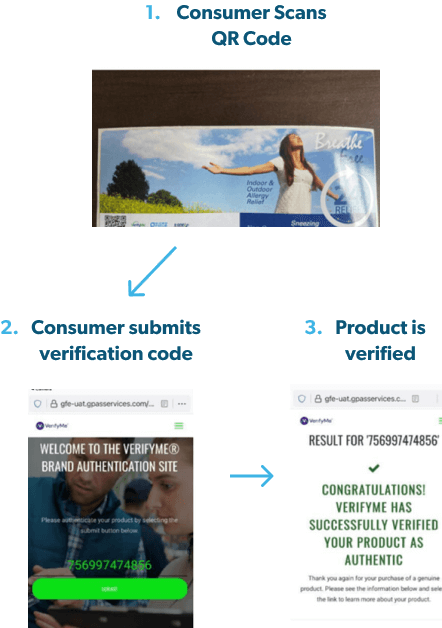
Custom Track and Trace Solutions
Track and trace security systems are unique product identification solutions that can be applied to individual products, cases, pallets, or shipping containers. The unique markers can be scanned at any point and the information will be uploaded to centrally located data management systems.
Brand owners and enforcement teams can access information collected with the data management systems at any time to track and authenticate their products at any point in the supply chain, from production to the retail shelf. They are commonly used to detect tampering with unique tracking identifications.
TRACK & TRACE SECURITY LABEL SOLUTIONS
- End-user verification builds customer confidence and brand loyalty
- Early detection of counterfeiting or diversion in a supply chain
- Labels are deterrents to counterfeiters
- Ability to have targeted product recalls
- Trace security labeling assists in return warranty verification
- Authenticate product labels
Questions to think about…
Is it a counterfeiting or diversion issue?
Authenticity, track and trace, safety / health concerns, E2E workflow integration
Who will be the authenticators?
Consumer engagement or inspectors
Should we go Covert or Overt?
Simple to no tools vs dedicated equipment
Intended uses of generated data?
Desired actions to be taken with generated data